Navigating the Forefront of Cybersecurity: 4 Investments in AI Changing cybersecurity
These are the recent largest funding announcements in AI cybersecurity.
Cybersecurity remains a top concern for businesses of all sizes.
According to Cybersecurity Ventures global spending on cybersecurity will grow continue growing 15 percent year-over-year to 2025.
Gartner predicts by 2024 at least 50% of organizations will use AI-driven security operations centers (SOCs) to detect cyberattacks more quickly than traditional methods allow
Innovations in this domain are not only about defense but also about staying one step ahead of potential threats.
In this blog post, we dive deep into four leading-edge cybersecurity companies, each offering different solutions to safeguard our digital future.
From transaction monitoring to threat intelligence, these trailblazers are redefining the paradigms of security in the era of AI and cloud computing.
1. ThetaRay - Transaction monitoring
ThetaRay to fight money laundering ThetaRay develops a transaction monitoring platform to identify signs of money laundering.
Stands out with its state-of-the-art cloud-based transaction monitoring and screening solution. Harnessing the power of its patented AI technology, the platform enables swift and precise monitoring of financial transactions.
Funding details:

2. Horizon3.ai - Automated pentesting
Pentesting is an essential part of security testing. Typically compliance, such as SOC 2 Type 2 require a penetration test.
Horizon3.ai specializes in offering a platform that delivers autonomous penetration testing as a self-service SaaS. Their platform also assists customers in swiftly verifying their security posture, subsequently diminishing their exploitable attack surface.

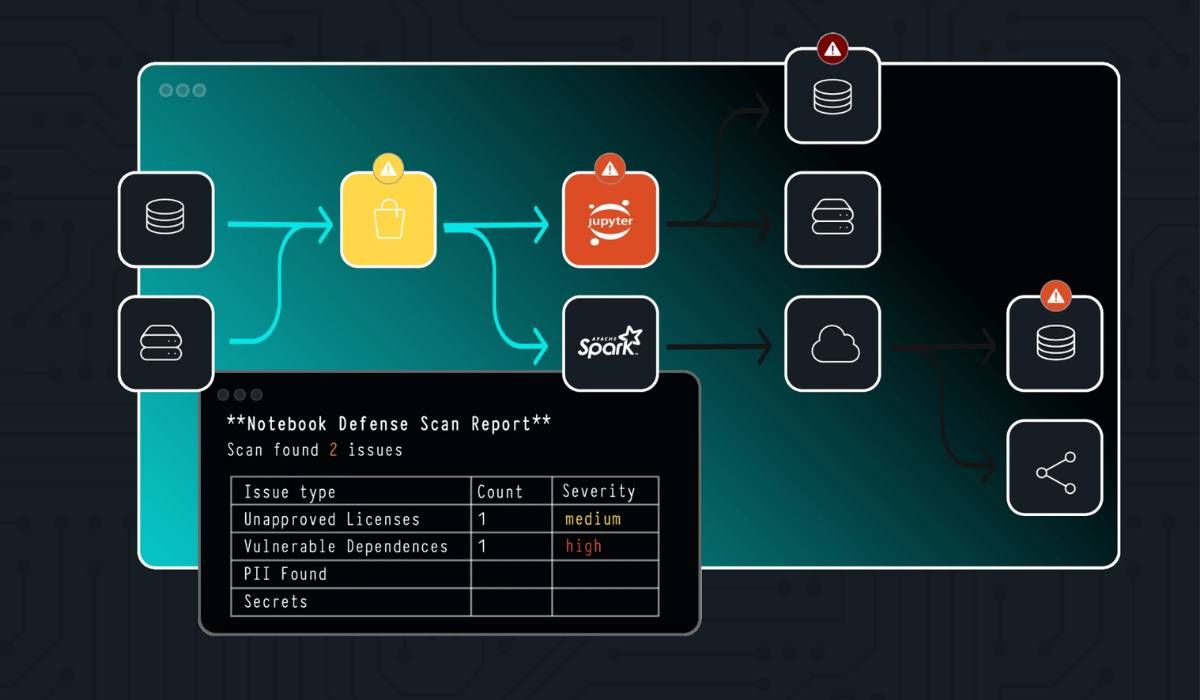
3. ProtectAI - AI/ML focused testing
ProtectAi is a cybersecurity platform that focuses on protecting machine learning models and artificial intelligence systems. Their goal is ensuring the delivery of secure and compliant ML models and AI applications.
They also purchased huntr.dev to create the first AI focused bug bounty platform
Funding details:
4. Cyware - Threat Intelligence
Cyware is AI-powered Cyber Fusion platforms for enterprises and MSSPs, and automated threat intelligence sharing for information sharing networks.
It achieves this by correlating actionable threat intelligence with essential security processes such as detection, threat hunting, vulnerability management, and incident response operations.
The modular nature of their Cyber Fusion platform gives security teams the liberty to either leverage its comprehensive capabilities or cherry-pick individual components, such as TIP, SOAR, and Collaborative Threat Response, granting unmatched adaptability in reshaping conventional SOCs.
Funding details:





